Privacy in 2026 is not a nice-to-have — it’s a necessity. Windows 11 phones home constantly. macOS ties your activity to an Apple ID. Mainstream browsers track everything. If you’ve decided that enough is enough, switching to a privacy-focused Linux distribution is the single most impactful step you can take to reclaim control of your digital life.
But “best Linux distros for privacy” means something different depending on what you’re actually trying to protect against. A journalist hiding sources has completely different needs from a developer who just wants to stop telemetry, or a security researcher doing penetration testing. This guide breaks it down by use case so you pick the right tool for your actual threat model — not just the most popular name on a list.
Why Linux is better for privacy — but not automatically private
Linux’s open-source nature means the code can be independently audited. There’s no hidden telemetry baked in at the OS level, no mandatory account sign-in, and no vendor lock-in. But out-of-the-box Linux is not automatically private. A stock Ubuntu installation still collects some usage data by default. Fedora phones home for updates. The privacy comes from choosing the right distribution and configuring it correctly.
The distros below are ranked and grouped by use case, not just by how often they appear on other lists.
Quick comparison — pick your use case first
| Use case | Best pick | Difficulty |
|---|---|---|
| Anonymous, leave-no-trace sessions | Tails | Beginner |
| Maximum isolation / high-value targets | Qubes OS | Advanced |
| Tor-routed daily driver | Whonix | Intermediate |
| Privacy-first everyday desktop | Fedora / PureOS | Beginner–Intermediate |
| Penetration testing + security research | Kali Linux / Parrot OS | Intermediate |
| Lightweight privacy on old hardware | Linux Kodachi | Intermediate |
1. Tails — Best for anonymous, leave-no-trace sessions
Best for: Journalists, activists, whistleblowers, or anyone who needs a clean session on an untrusted machine Difficulty: Beginner-friendly Based on: Debian
Tails is the gold standard for anonymous computing and has been for over a decade. It runs entirely from a USB stick or DVD, boots into a live session, routes all internet traffic through the Tor network by default, and — critically — writes nothing to the computer’s hard drive. When you shut it down, the session is completely gone. No traces, no logs, no history.
Tails stores your data in RAM instead of using a computer’s hard drive and erases all session information when you shut down. This makes it uniquely valuable for situations where you need to use a computer you don’t own or fully trust — a library PC, a colleague’s laptop, or any device that might be inspected later.
Tails also ships with a curated set of privacy tools pre-installed: the Tor Browser, KeePassXC for passwords, OnionShare for anonymous file sharing, and Thunderbird with Enigmail for encrypted email. Everything is configured to leak as little as possible by default.
What’s good:
- Zero footprint on the host machine — nothing is written to disk
- All traffic goes through Tor automatically, no configuration needed
- Ships with the essential privacy toolkit out of the box
- Beginner-friendly despite its powerful privacy guarantees
- Free, open-source, and actively maintained
Limitations:
- Not a daily driver — no persistent storage by default (though persistent encrypted storage is available as an option)
- Tor routing makes some websites slow or inaccessible
- Not designed for heavy workloads or software development
Download: tails.boum.org
2. Qubes OS — Best for maximum isolation
Best for: High-value targets: security researchers, lawyers, executives, journalists handling sensitive sources Difficulty: Advanced Based on: Fedora / Debian (via Xen hypervisor)
Qubes OS uses a compartmentalisation approach where different tasks run in separate virtual machines, called qubes. This means that if one part of your system is compromised, the damage stays contained. Think of it as air-gapping within a single machine — your banking, your work, your personal browsing, and your internet-connected apps all run in separate isolated environments that cannot see each other. Oracle
This is not just a privacy feature — it’s a fundamentally different security architecture. Even if a malicious PDF you opened in your “work” qube tries to exfiltrate data, it has no access to your “personal” or “vault” qubes. The damage is contained.
As of 2025, version 4.2 introduces enhanced hardware compatibility and faster Qube management tools, making it even more user-friendly. Oracle
What’s good:
- The most secure desktop OS architecture available to ordinary users
- Compartmentalisation means a compromised app cannot access the rest of your system
- Supports Whonix integration for Tor-routed qubes
- Actively developed and trusted by security professionals worldwide
Limitations:
- Steep learning curve — expect a week before it feels natural
- Requires powerful hardware: 16GB RAM minimum recommended, 32GB+ preferred
- Some hardware (especially newer laptops) can have compatibility issues
Download: qubes-os.org
3. Whonix — Best Tor-routed daily driver
Best for: Users who want Tor-level anonymity without living off a USB stick Difficulty: Intermediate Based on: Debian
Whonix is designed to work on top of the host OS and runs on two virtual machines: Whonix-Workstation is completely isolated and can only talk to the Whonix-Gateway, which routes all your connections to the anonymous Tor network. Such isolation creates additional protection from unexpected DNS leaks and malware attacks.
The two-VM design is clever: even if malware somehow compromises your Workstation VM, it cannot discover your real IP address because it has no direct internet access — all traffic must go through the Gateway, which only speaks Tor. DNS leaks, one of the most common ways anonymity breaks down, are structurally impossible in this architecture.
Whonix works inside VirtualBox, KVM, or as part of Qubes OS. It’s the recommended setup for people who need Tor-level anonymity but also need a persistent, functional working environment.
What’s good:
- Structural protection against DNS leaks — not just configuration-based
- Can be used as a persistent daily environment, unlike Tails
- Pairs perfectly with Qubes OS for maximum security
- Actively developed with regular security updates
Limitations:
- Requires a host OS and virtualisation software — adds setup complexity
- Tor routing means slower browsing speeds
- Not beginner-friendly out of the box
Download: whonix.org
4. Fedora — Best privacy-focused daily driver for most people
Best for: Developers and everyday users who want a practical, modern desktop with strong privacy defaults Difficulty: Beginner–Intermediate Based on: RPM / independent (upstream of RHEL)
Fedora might surprise you on a privacy list — it’s not a specialist privacy distro. But it’s arguably the best balance between a fully functional modern desktop and strong privacy practices for the average user in 2026.
Fedora ships with SELinux enforcing by default — one of the strongest mandatory access control systems available on Linux. It uses Wayland by default, which has better application isolation than X11. It has minimal telemetry compared to Ubuntu, and what it does collect is optional and clearly documented. The Fedora project has a well-established privacy policy and a track record of responding quickly to security vulnerabilities.
For a daily driver that balances ease of use with privacy, Fedora Workstation is a top recommendation for users who want current kernels and an active ecosystem.
What’s good:
- SELinux enforcing by default — significantly raises the bar for attackers
- Wayland by default — better application sandboxing than X11
- Fast security updates — Fedora often patches vulnerabilities before Ubuntu
- Huge software repository, excellent hardware support
- No Snap packages — avoids Ubuntu’s controversial telemetry debate
Limitations:
- Shorter release cycle (13 months) — you’ll update to a new version more often than Ubuntu LTS users
- Not designed specifically for anonymity — use Tor Browser manually if needed
- Some proprietary drivers require third-party repos
Download: fedoraproject.org
5. PureOS — Best out-of-the-box privacy desktop
Best for: Users who want privacy defaults set up for them, without configuration Difficulty: Beginner Based on: Debian
PureOS is the clearest out-of-the-box choice for a privacy-focused desktop in 2026 because it enforces free-software-only repositories and ships privacy tools by default. It’s developed by Purism, the same company that makes the Librem laptops and the Librem 5 Linux phone, and it’s endorsed by the Free Software Foundation. linuxlap
PureOS ships with the GNOME desktop, uses the PureBrowser (a hardened Firefox fork) as its default browser, and enforces a strict free-software-only repository policy — meaning no proprietary drivers or blobs are installed without your explicit knowledge and consent. For users who want a clean, ethical, private desktop without spending hours configuring it, PureOS is hard to beat.
What’s good:
- Privacy tools configured by default — no post-install hardening needed
- Free-software-only repository policy — maximum software auditability
- FSF-endorsed — strong open-source ethics credentials
- Based on Debian stable — rock solid and reliable
Limitations:
- The no-proprietary-firmware policy can cause hardware compatibility issues (especially WiFi on some laptops)
- Smaller community than Ubuntu or Fedora
- Best paired with Purism hardware for the full experience
Download: pureos.net
6. Parrot OS Home Edition — Best for privacy-aware developers
Best for: Developers and everyday users who want privacy tools alongside a functional desktop Difficulty: Beginner–Intermediate Based on: Debian
Parrot OS Home Edition is aimed at daily use, privacy, and software development. It gives users a practical mix of privacy and daily desktop comfort, and works well for people who want one system for learning, writing, browsing, and coding.
Parrot comes in two flavours — Security (the full penetration testing suite, covered below) and Home, which focuses on privacy and development. Home Edition includes AnonSurf, Parrot’s one-command tool that routes all your traffic through Tor, and comes with a hardened Firefox, OnionShare, and other privacy utilities pre-installed. It’s lighter than Kali and more privacy-conscious than a standard Ubuntu install.
What’s good:
- AnonSurf makes Tor routing a single command away
- Lighter than Kali — more suitable as a daily driver
- Excellent for developers who also care about their privacy
- Ships with privacy tools configured and ready to use
Limitations:
- Smaller community than Ubuntu or Fedora
- AnonSurf is convenient but not as architecturally secure as Whonix’s approach
- Security Edition (not Home) is what you want for penetration testing
Download: parrotsec.org
7. Kali Linux — Best for penetration testing and security research
Best for: Security professionals, ethical hackers, CTF competitors, cybersecurity students Difficulty: Intermediate Based on: Debian
Kali Linux is the industry standard for penetration testing. Built on Debian, it is the most widely used Linux distro for cybersecurity and security tests, featuring a wide range of tools for penetration testing, digital forensics, network analysis, and security evaluations.
The 2026 release of Kali includes over 600 pre-installed security tools covering everything from network scanning (Nmap, Wireshark) to exploitation frameworks (Metasploit), password auditing (Hashcat, John the Ripper), wireless testing (Aircrack-ng), and web application testing (Burp Suite, OWASP ZAP). Kali also now ships with a dedicated AI-assisted tooling suite for automated vulnerability scanning.
It’s worth being clear: Kali is a security testing tool, not a personal privacy OS. It doesn’t route your traffic through Tor by default and isn’t designed to protect you from surveillance. Use it for what it’s built for — testing and research.
What’s good:
- The most complete penetration testing toolkit available anywhere
- Regularly updated with new tools and CVE-specific modules
- Works well as a live USB, VM, or full install
- Strong community, excellent documentation, and certifications (OSCP, CEH) built around it
Limitations:
- Not a privacy OS — don’t use it as a daily driver expecting anonymity
- Default security posture is loose (designed for testing, not hardening)
- Root-oriented approach requires care in shared environments
Download: kali.org
8. Linux Kodachi — Best lightweight all-in-one privacy OS
Best for: Users who want a comprehensive privacy toolkit on a single bootable USB Difficulty: Intermediate Based on: Debian / Xubuntu
Linux Kodachi automatically establishes a VPN connection, Tor browser, and DNScrypt service, providing maximum safety and privacy. Like Tails, Kodachi stores your data in RAM and provides easy setup using a USB stick, DVD, or SD card. Kodachi puts extra emphasis on security offering pre-installed tools such as firewall utilities, intrusion detection systems, malware scanners, and encryption tools. Linuxiac
Kodachi’s appeal is its density of privacy features in a single, usable package. Where Tails is ruthlessly minimal in exchange for its no-trace guarantee, Kodachi is more like a full privacy-hardened desktop that happens to also run from a USB. It includes a built-in panic button that wipes the RAM and shuts the system down — a feature that few other distros offer.
What’s good:
- All-in-one VPN + Tor + DNS encryption configured out of the box
- Panic button feature for emergency data wiping
- More feature-rich than Tails as a working environment
- Runs from USB with optional persistence
Limitations:
- Smaller development team than Tails or Qubes — updates can lag
- The simultaneous VPN + Tor configuration isn’t always optimal for anonymity (Tor over VPN vs. VPN over Tor has important implications)
- Less audited than Tails or Whonix
Download: digi77.com/linux-kodachi
Which one should you actually use?
You’re new to Linux and just want better privacy than Windows: Start with Fedora or PureOS. They work like normal desktops but with significantly stronger default privacy settings. Add the Tor Browser manually for sensitive browsing.
You need occasional anonymous sessions (journalism, research, sensitive communications): Use Tails from a USB stick for those sessions, and your normal OS for everything else.
You handle genuinely sensitive data every day: Look seriously at Qubes OS. The learning curve is real, but the compartmentalisation it provides is unmatched. Pair it with Whonix qubes for Tor-routed work.
You’re a developer who wants privacy without sacrificing usability: Parrot OS Home or Fedora are your best bets. Both support modern development toolchains while keeping privacy front of mind.
You’re learning cybersecurity or doing penetration testing: Kali Linux is the answer. Just understand it’s a testing tool, not a privacy OS.
A note on threat modelling
The best privacy setup is the one that matches your actual threat model. There’s no single “most private” Linux distro — it depends entirely on who you’re protecting your data from, what you’re trying to keep private, and how much friction you’re willing to accept in your daily workflow.
A good starting point for anyone is: full disk encryption (all of the distros above support this), a DNS provider that doesn’t log queries, and a habit of using Tor Browser or a reputable VPN for sensitive browsing — regardless of which distro you choose.
Privacy is a practice, not just a software choice.
The best Linux distros for privacy
How to Install Nginx on Ubuntu (26.04, 24.04 and 22.04)
Updated: May 2026 | Covers APT and official Nginx repository methods | Ubuntu 26.04 (Resolute Raccoo…
KLV-Airedale: The Void Linux Distro That Thinks Like Puppy Linux
Most Linux distributions fit neatly into one of two camps: the polished mainstream distros that hold…
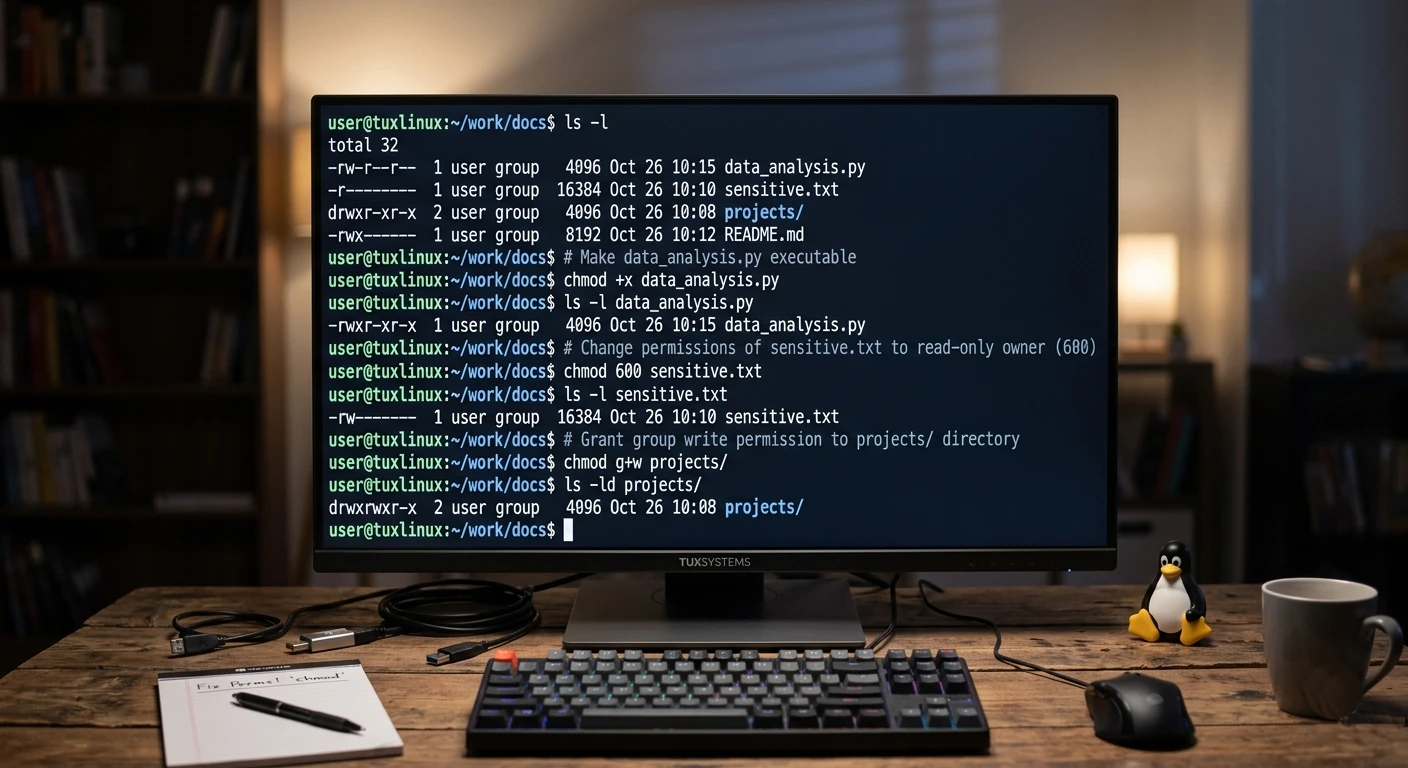
Mastering File Permissions in Linux (Without the Headache)
If you’ve ever felt a little lost staring at output like -rwxr-xr–, don’t worry—you’re not alone. F…
Beyond TLP: The Ultimate Guide to Linux Laptop Battery Optimization in 2026
For years, the standard advice for any Linux laptop user has been: “Just install TLP and forge…
How to Install VS Code on Ubuntu (24.04, 22.04 and 20.04)
Updated: May 2026 | Three methods covered | Works on all active Ubuntu LTS releases VS Code is the m…
Best Linux Distro for Old Laptops in 2026 (Your Windows 10 Replacement Guide)
Updated: May 2026 | Tested on hardware with 1GB–8GB RAM | Covers laptops from 2010–2020 Windows 10 s…