Published: May 2026 | Affects every major Linux distribution built since 2017
A critical Linux kernel vulnerability has been publicly disclosed that security researchers are calling one of the most significant privilege escalation flaws in years. Tracked as CVE-2026-31431 and nicknamed “Copy Fail”, it allows any unprivileged local user to obtain full root access on virtually every major Linux distribution — using nothing more than a 732-byte Python script.
The vulnerability was publicly disclosed on 29 April 2026 and affects every mainstream Linux distribution shipping a kernel built since 2017. Patches are now being rolled out, but the window between disclosure and patching is exactly when attackers move fast.
Here is everything you need to know.
What is Copy Fail?
Copy Fail is a logic bug in the Linux kernel’s authencesn cryptographic template. It lets an unprivileged local user trigger a deterministic, controlled 4-byte write into the page cache of any readable file on the system.
That might sound abstract, so here is what it means in practice. When Linux loads and runs a program, it reads it from the kernel’s page cache — an in-memory copy of the file. Copy Fail allows an attacker to modify that in-memory copy without ever touching the file on disk. Because the page cache represents the in-memory version of executables, modifying it effectively alters binaries at execution time without touching disk. This enables attackers to inject code into privileged binaries such as /usr/bin/su and thereby gain root privileges.
The on-disk file remains completely clean. Standard file integrity checks, checksums, and antivirus tools that scan the filesystem see nothing wrong — because nothing on disk has changed.
Why this is worse than Dirty Cow and Dirty Pipe
Security veterans will immediately compare Copy Fail to two previous high-profile Linux privilege escalation vulnerabilities: Dirty Cow (2016) and Dirty Pipe (2022). Copy Fail is in the same class — but in several ways it is more dangerous than both.
Dirty Cow required winning a race condition in the VM subsystem’s copy-on-write path. It often needed multiple attempts and sometimes crashed the system. Dirty Pipe was version-specific and required precise pipe buffer manipulation. Copy Fail is a straight-line logic flaw. It triggers without races, retries, or crash-prone timing windows.
In other words, it is reliable, repeatable, and consistent. There is no luck involved, no timing window to hit, no chance of crashing the system in the attempt. The same exact script works on every tested distribution and architecture, including Ubuntu, Amazon Linux, RHEL, and SUSE. No per-distro offsets. No recompilation. No version checks in the exploit.
The proof of concept exploit is a 10-line, 732-byte Python script capable of editing a setuid binary to gain root on almost all Linux distributions released since 2017. It requires only Python 3.10+ and standard library modules — no compiled payloads, no external dependencies.
How the vulnerability works (technical summary)
The flaw originates from an in-place optimization introduced in 2017, where the kernel reuses source memory as the destination during cryptographic operations. By abusing the interaction between the AF_ALG socket interface and the splice() system call, an attacker can perform a controlled 4-byte write into the kernel’s page cache of any readable file.
The root cause is in how the kernel’s AEAD (Authenticated Encryption with Associated Data) socket interface handles memory. When the optimization was introduced in 2017, page cache pages ended up placed in a writable destination scatterlist. The design assumes every AEAD algorithm will confine its writes to the intended destination, but nothing in the API enforces this, and nothing documents it as a requirement. Unfortunately, one AEAD algorithm breaks this silent invariant.
The result: a logic flaw that sat undetected for nine years, hiding in plain sight inside the kernel’s cryptographic subsystem — one of the most heavily reviewed areas of the codebase.
Who discovered it?
The bug was surfaced by an AI system in about an hour of scan time against the Linux crypto/ subsystem, with one operator prompt and no harnessing. The discovery was made by Theori and Xint, two well-regarded offensive security research teams.
Probably because crypto/ is heavily reviewed from a crypto lens, looking for properties like IND-CPA security, side channels, and parameter validation. Copy Fail is fundamentally about where the memory came from and whether the kernel should ever be writing through it — a different type of question, and probably why it went missed.
Who is affected?
The vulnerability affects virtually all Linux distributions running kernels released from 2017 until patched versions are applied, including but not limited to Ubuntu 24.04 LTS, Amazon Linux 2023, Red Hat Enterprise Linux 10.1, and SUSE 16, as well as other distributions like Debian, Fedora, and Arch Linux.
The threat is especially serious in cloud and containerised environments. The prevalence of Linux in cloud environments means the vulnerability has a significant impact. Copy Fail poses a serious risk to containerised environments, as Docker, LXC, and Kubernetes grant processes inside a container access to the AF_ALG subsystem if the algif_aead module is loaded.
The bug is of most immediate concern to those using multi-tenant Linux systems, shared-kernel containers, or CI runners that execute untrusted code. The vulnerability also represents a potential container escape primitive that could affect Kubernetes nodes, because the page cache is shared across the host.
It is worth noting that this vulnerability is not remotely exploitable in isolation, but becomes highly impactful when chained with an initial access vector such as SSH access, malicious CI job execution, or container footholds. An attacker needs some form of local or container access first — but in shared cloud environments, that bar is often lower than it sounds.
Has it been exploited in the wild?
CISA added CVE-2026-31431 to its Known Exploited Vulnerabilities (KEV) catalog. Federal Civilian Executive Branch agencies have been advised to apply the fixes by May 15, 2026. Active exploitation has so far been observed primarily in proof-of-concept testing, but with a working public exploit and CISA’s KEV listing, real-world attacks are expected to escalate rapidly.
How to check if you are vulnerable
Run the following command to check your current kernel version:
bash
uname -rFixes have been made available in Linux kernel versions 6.18.22, 6.19.12, and 7.0. If your kernel is older than these versions and your distribution has not yet pushed a patched package, you are vulnerable.
How to protect yourself right now
Step 1 — Apply kernel updates immediately
Check your distribution’s security tracker and apply available kernel updates as soon as they are published. This is the only complete fix.
bash
# Debian / Ubuntu
sudo apt update && sudo apt upgrade
# Fedora / RHEL / AlmaLinux / Oracle Linux
sudo dnf update kernel
# Arch Linux
sudo pacman -SyuStep 2 — Apply the interim mitigation if no patch is available yet
CERT-EU strongly recommends applying the interim mitigation immediately, prioritising Kubernetes nodes and CI/CD runners exposed to untrusted workloads. Disable the algif_aead kernel module persistently on all affected systems until a patched kernel is available:
bash
echo "install algif_aead /bin/false" > /etc/modprobe.d/disable-algif.conf
rmmod algif_aead 2>/dev/null || trueThis workaround does not affect dm-crypt/LUKS, kTLS, IPsec/XFRM, OpenSSL, GnuTLS, NSS, or SSH. It may affect applications explicitly configured to use the afalg engine or that bind aead/skcipher/hash sockets directly. Exposure can be assessed with:
bash
lsof | grep AF_ALGStep 3 — Audit container and Kubernetes environments
If you run containers or Kubernetes nodes, treat any container remote code execution as a potential host compromise until patched. Enforce rapid node recycling after any compromise indicators are detected.
The bigger picture
Copy Fail is not just a single vulnerability story — it is a warning about the direction Linux kernel security is heading. After the Linux kernel team became a CVE Numbering Authority in 2024, disclosure rates accelerated dramatically, with the 2024 total reaching 3,529 kernel CVEs — a tenfold increase from prior years. With 8–9 new kernel CVEs appearing daily, distinguishing critical threats from noise has become a full-time job.
Copy Fail cuts through that noise because of its combination of properties that rarely appear together: universal applicability across distributions, no race condition required, a tiny and dependency-free exploit, stealth against on-disk detection tools, and cross-container impact on shared hosts. It is the kind of vulnerability that resets assumptions.
The fix for your system is straightforward — patch or disable the module. The harder fix is the cultural one: treating kernel updates as genuinely urgent, not something to schedule around a maintenance window three weeks from now.
Summary
| Property | Detail |
|---|---|
| CVE | CVE-2026-31431 |
| Nickname | Copy Fail |
| Severity | High — CVSS 7.8 |
| Disclosed | 29 April 2026 |
| Affected kernels | 2017 – present (pre-patch) |
| Fixed in | Kernel 6.18.22, 6.19.12, 7.0 |
| Remotely exploitable | No — requires local or container access |
| CISA KEV listed | Yes |
| Interim mitigation | Disable algif_aead module |
How to Install Nginx on Ubuntu (26.04, 24.04 and 22.04)
Updated: May 2026 | Covers APT and official Nginx repository methods | Ubuntu 26.04 (Resolute Raccoo…
KLV-Airedale: The Void Linux Distro That Thinks Like Puppy Linux
Most Linux distributions fit neatly into one of two camps: the polished mainstream distros that hold…
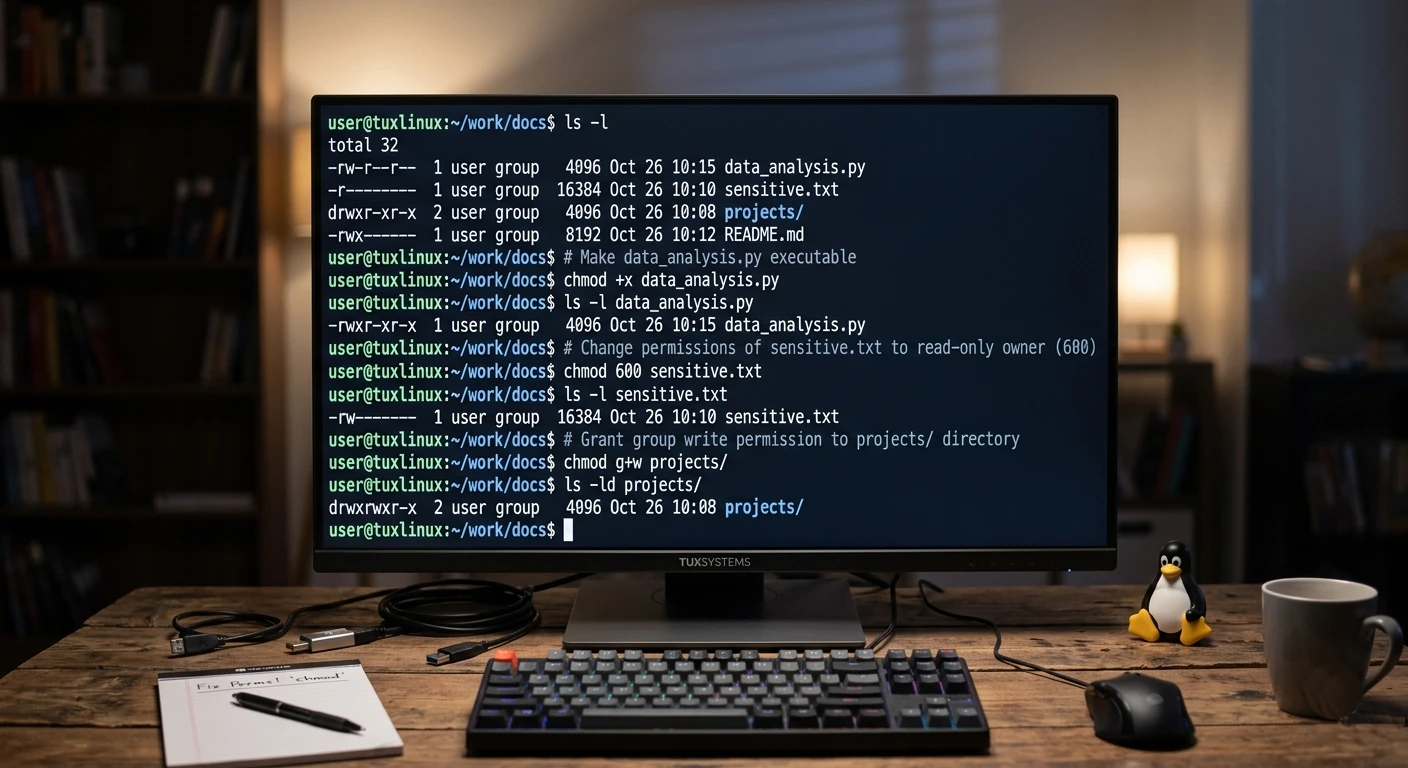
Mastering File Permissions in Linux (Without the Headache)
If you’ve ever felt a little lost staring at output like -rwxr-xr–, don’t worry—you’re not alone. F…
Beyond TLP: The Ultimate Guide to Linux Laptop Battery Optimization in 2026
For years, the standard advice for any Linux laptop user has been: “Just install TLP and forge…
How to Install VS Code on Ubuntu (24.04, 22.04 and 20.04)
Updated: May 2026 | Three methods covered | Works on all active Ubuntu LTS releases VS Code is the m…
Best Linux Distro for Old Laptops in 2026 (Your Windows 10 Replacement Guide)
Updated: May 2026 | Tested on hardware with 1GB–8GB RAM | Covers laptops from 2010–2020 Windows 10 s…

How to Secure Smart Home Devices: A Beginner’s Complete Guide

Edge Computing: The Future of Data Processing and Connectivity