Security-Enhanced Linux (SELinux) is one of the most powerful—and often misunderstood—security mechanisms in the Linux ecosystem. Frequently seen as a complex obstacle, many system administrators are tempted to disable it rather than understand it. However, taking the time to learn SELinux reveals a robust, fine-grained access control system that provides a formidable defense against system compromises.
This article will break down SELinux from its core philosophy to practical, real-world management.
The “Why”: From Discretionary to Mandatory Access Control
To understand SELinux, you must first understand the standard Linux security model it enhances. By default, Linux uses Discretionary Access Control (DAC).
Discretionary Access Control (DAC) 🛡️ In a DAC model, the owner of an object (like a file or directory) has the discretion to grant or deny access to others. This is managed through the familiar user, group, and other permissions (rwx). If you own a file, you can chmod 777 it, and anyone can read, write, and execute it.
- The Weakness: The primary weakness of DAC is its reliance on user-level decisions. If a user’s account is compromised, the attacker gains all the privileges of that user. If that user is
root, the attacker owns the entire system. A vulnerable web server running as theapacheuser can be exploited to read or modify any file theapacheuser has access to, potentially including sensitive configuration files or user data in other directories.
Mandatory Access Control (MAC) 👮 SELinux implements Mandatory Access Control (MAC). In a MAC model, access is dictated by a system-wide policy established by the administrator. This policy is mandatory and cannot be overridden by individual users, not even root.
- The Strength: Every single action, from a process opening a file to one process communicating with another, is checked against the SELinux policy. If there is no explicit rule allowing the action, it is denied. This means that even if an attacker compromises a web server running as
root, SELinux will prevent that process from doing anything outside of its strictly defined role, like sending emails or reading files in/home. The compromised process is effectively trapped in a security sandbox defined by the policy.
The Architecture: How SELinux Works
SELinux isn’t a standalone program. It’s a kernel module integrated through the Linux Security Modules (LSM) framework. The LSM framework provides a set of hooks within the kernel’s core functions (e.g., open(), execve(), socket()). When one of these functions is called, the hook passes the action to SELinux for a decision.
The core components are:
- Subjects: The actors on the system, which are almost always processes.
- Objects: The resources that subjects act upon, such as files, directories, sockets, and devices.
- SELinux Policy: A massive set of rules that defines the allowed interactions between subjects and objects. This is the heart of SELinux.
- Security Server: The component within the kernel that caches policy decisions. When an action is attempted, the kernel asks the Security Server, “Is subject ‘A’ allowed to perform action ‘B’ on object ‘C’?” This avoids having to read the policy from disk for every single operation.
Core Concepts: The Language of SELinux
To manage SELinux, you need to understand its vocabulary. The most important concept is the security context.
Security Contexts (The “Nametags”) 🏷️
Every subject (process) and object (file, etc.) on an SELinux-enabled system has a security context, or “label,” attached to it. This context is the primary information the policy uses to make decisions. You can view these contexts with the -Z flag in many common commands (ls -Z, ps -Z).
A context is composed of four colon-separated fields: user:role:type:level.
unconfined_u:object_r:httpd_sys_content_t:s0
- User: An SELinux user identity. This is not the same as a Linux user account. It defines the roles a user can assume.
- Role: Defines a set of allowed types for a user. The role acts as an intermediary between the user and the type.
- Type: This is the most important part of the context. The SELinux policy is primarily a policy of Type Enforcement (TE). The vast majority of rules are written in the format: “Allow processes with type
Ato access files with typeB.” - Level: Used for Multi-Level Security (MLS), which provides an even stricter security model based on hierarchical levels (e.g., Unclassified, Secret, Top Secret). In the default targeted policy, this is typically fixed at
s0.
For most day-to-day administration, you will almost exclusively focus on the type.
Modes of Operation 🚦
SELinux can operate in one of three modes:
- Enforcing: The default and most secure mode. The SELinux policy is actively enforced. Any action not explicitly allowed by the policy is denied, and the denial is logged.
- Permissive: SELinux does not enforce the policy. All actions are allowed, but any action that would have been denied in enforcing mode is logged. This mode is invaluable for troubleshooting and developing new policies.
- Disabled: The SELinux kernel module is completely disabled. A reboot is required to switch to or from this mode. Disabling SELinux is strongly discouraged.
You can check the current mode with sestatus or getenforce. You can temporarily switch between Enforcing and Permissive with setenforce 1 (Enforcing) and setenforce 0 (Permissive).
Booleans
The SELinux policy is not monolithic. It contains a set of on/off switches called booleans that allow you to change parts of the policy at runtime without needing to recompile it. For example, there’s a boolean httpd_can_network_connect that controls whether the Apache web server can initiate outgoing network connections.
- To list all booleans related to httpd:
getsebool -a | grep httpd - To turn a boolean on or off permanently:
setsebool -P httpd_can_network_connect on
Practical Management and Troubleshooting 🔍
This is where theory meets reality. Most SELinux issues arise when a file gets the wrong security context.
A Classic Example: Changing Apache’s Web Root
Let’s say you want to serve your website from /srv/www instead of the default /var/www/html.
- You create the directory:
mkdir -p /srv/www - You put an
index.htmlfile inside. - You edit your Apache configuration (
/etc/httpd/conf/httpd.conf) to pointDocumentRootto/srv/www. - You restart Apache, and it fails. You check the web server logs and see “Permission Denied” errors, even though your file permissions are
755.
This is a classic SELinux problem. Let’s diagnose it.
First, check the SELinux logs, which are usually found in /var/log/audit/audit.log. You’ll see an AVC (Access Vector Cache) denial. A more user-friendly tool is sealert.
Bash
sealert -a /var/log/audit/audit.log
The output will tell you exactly what happened: a process with the context httpd_t (the Apache process) was denied access to a file with the context default_t or var_t (your new directory).
Why did this happen? Let’s compare the contexts:
Bash
# ls -Zd /var/www/html
drwxr-xr-x. root root system_u:object_r:httpd_sys_content_t:s0 /var/www/html
# ls -Zd /srv/www
drwxr-xr-x. root root unconfined_u:object_r:var_t:s0 /srv/www
The original directory has the type httpd_sys_content_t. The SELinux policy has a rule allowing httpd_t to access files labeled with httpd_sys_content_t. Your new directory, however, inherited the context of its parent (/srv), which is var_t. There is no rule allowing httpd_t to access var_t.
The Fix:
You need to tell SELinux that /srv/www and everything inside it should have the httpd_sys_content_t context.
- Define the new file context rule: Use the
semanagecommand to add a permanent rule to the SELinux policy database.Bashsemanage fcontext -a -t httpd_sys_content_t "/srv/www(/.*)?"This command tells SELinux that/srv/wwwand everything inside it ((/.*)?) should be labeled with thehttpd_sys_content_ttype. - Apply the context: The
semanagecommand only defines the rule. Now you must apply it to the filesystem usingrestorecon.Bashrestorecon -Rv /srv/wwwTherestoreconcommand reads the file context rules and “restores” the contexts on the filesystem to match the policy. The-Ris for recursive, and-vis for verbose.
Now if you check the context again (ls -Zd /srv/www), you’ll see it’s correct. Restart Apache, and it will work perfectly.
Key Troubleshooting Commands
sestatus: Get the overall status of SELinux.ls -Z,ps -Z,id -Z: View contexts of files, processes, and users.ausearch -m AVC -ts recent: Search audit logs for recent denials.audit2why: Translates cryptic audit logs into human-readable explanations.semanage fcontext -l: List all known file context definitions.restorecon: Apply file context definitions to the filesystem.
Conclusion
SELinux transforms Linux security from a user-controlled model to a policy-controlled one. It provides a robust safety net that contains breaches and limits the damage an attacker can do, even if they gain root privileges.
While it has a steep learning curve, the logic is consistent: everything has a context (a label), and the policy dictates what labeled subjects can do to labeled objects. Most problems boil down to mislabeled files. By mastering the core concepts of contexts and the tools like semanage and restorecon, you can turn SELinux from a source of frustration into one of the most powerful tools in your security arsenal. The correct response to an SELinux denial is almost never setenforce 0; it’s an opportunity to understand and properly configure your system’s security policy.

Building an Open-Source Smart Home: Tools and Platforms You Need
Deepin 25.1 Is Here — And It’s Quietly Becoming one of the Most AI-Integrated Linux Desktop Yet
Linux distributions have experimented with AI before—but most of them treat it like an add-on. Deepi…
Linux Says Goodbye to the i486 Era – The End of a Computing Legend
Linux i486 support removed — a sentence that marks the end of one of the longest-running hardware le…
Linux for Beginners: Complete 2026 Guide (Install, Basics, Tips)
This guide to Linux for beginners is designed to strip away the complexity and show you how modern, …
25 Practical Linux Terminal Tips and Tricks You’ll Actually Use (2026 Guide)
Why Learning the Linux Terminal Still Matters Linux Terminal Tips and TricksEven in 2026, the Linux …
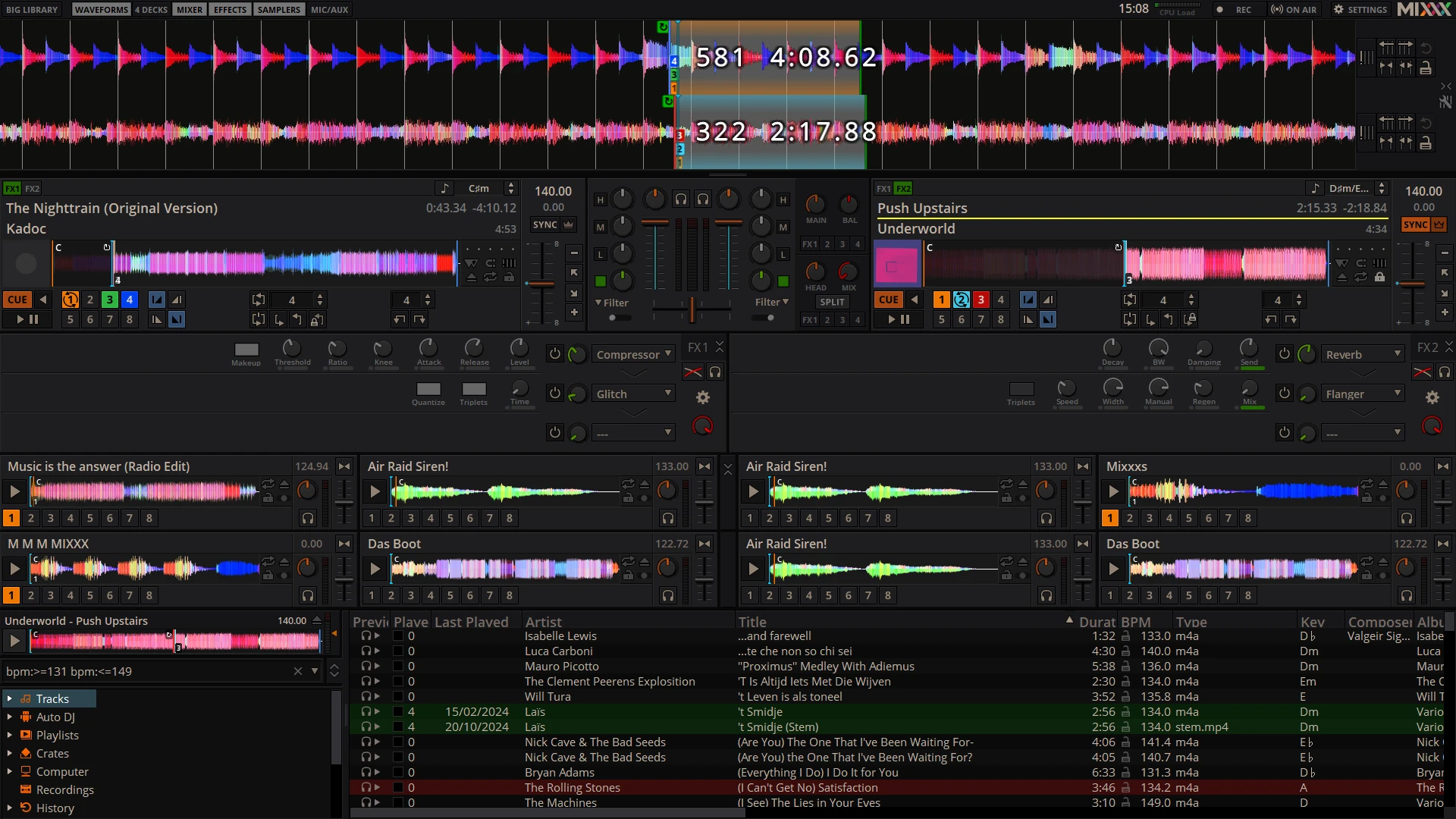
Mixxx 2.5.6 Released: Better Controller Support and Improved Effects for Linux DJs
The open-source DJ software scene continues to evolve, and the latest update to Mixxx brings meaning…
How to Automatically Clean Disk Space in Linux (Set Up Smart Auto-Cleanup in Minutes)
If your Linux system keeps running out of disk space, you’re not alone. Over time, cached packages, …